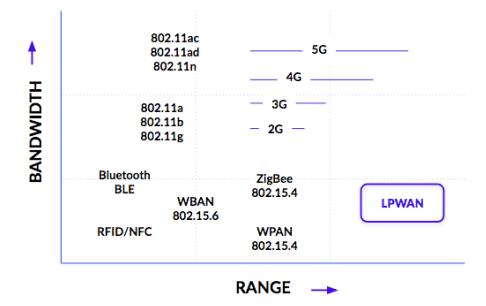
The most important ability of IoT devices is that of communication. there are different protocols with different areas of application. While WiFi, Bluetooth, Zigbee or other radio standards are often used for short distances in the home, devices have to be located elsewhere use alternative technologies. Such a group of technologies is LoRaWAN transmission. However, these have the advantage of a significantly longer range and better energy efficiency than most other radio standards at the expense of bandwidth. The picture below shows LoRaWAN compared to some other wireless communication protocols. LoRaWAN technologies are mostly used when end devices are installed in locations that only work with other technologies that are difficult to achieve, or when energy efficiency is of great importance. In this LoRaWAN is used as LPWAN technology.
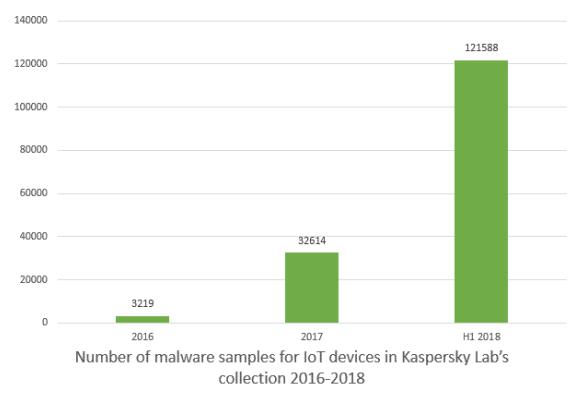
However, range and power consumption are not the only important points in the IoT. One issue that is often neglected is the security of networked devices. Between 2017 and 2018 alone, the number of known malware for IoT devices increased almost quadrupled. But malware isn’t the only threat. Lots of IoT devices send data inadequately protected, causing attacks on that data and thus also on the IoT infrastructure. Espionage, manipulation of data and the complete takeover of systems are exemplary attack scenarios.
Another relevant topic in IoT security is firmware updates; they enable manufacturers to bring new functions to devices and, in the event of security incidents, to remedy them without the user having to become active. It is extremely important that the updates are also carried out in a secure manner so that attackers are unable to inject fake firmware into a device.
Combining firmware updates and end devices that use a LoRaWAN protocol for data transmission creates a completely new challenge. While for IP-based technologies, such as B. W-LAN, there are already some suggestions for specific protocols, updates via LoRaWAN are still largely unexplored. The reason that the classic protocols cannot be used can be found in the restrictions of LoRaWAN technologies. LoRaWAN, for example, has high limitations in terms of data rate and LoRaWAN transmission speed and has no standardized transport protocol, which compensates for losses in data transmission could.
1.1 The smart mailbox
In this work, a specific application is considered and various topics of IoT security are examined. A smart mailbox was developed, which notifies the user via their smartphone when mail is in the mailbox has been received.
1.1.1 Use case
The basic idea of the smart mailbox is to make sure that the user doesn’t constantly have to open his mailbox to find out if there is any mail in it. Instead, he should receive a notification on his mobile device as soon as there is mail is in the mailbox. This has the advantage that the time of the user is not unnecessary due to mailboxes that are far from the user or that rarely contain mail Is claimed.
The functions of the application are deliberately kept small because of the focus on security and energy efficiency. In addition, the application was developed as an “extension”. It should be possible to do this with little effort on the part of the user to install any letterboxes. Battery operation and a small form factor are thus also requirements for the project.
1.1.2 Examined topics with LoRaWAN transmission
As mentioned earlier, the focus of the work is on IoT security. In addition, energy efficiency is considered. From these priorities, there are several subtopics that are examined using the smart mailbox have been the first point is the secure, E2E-encrypted data LoRaWAN transmission. Especially With mailboxes in public areas, it is important that an attacker does not find out can determine whether and how much mail is in the mailbox. This prevents who can easily find out if a break-in would be worthwhile. Protection is also important against manipulation to prevent the user from receiving false information about the condition of the mailbox. In addition, it is examined to what extent the negotiation of cryptographic keys for these tasks is a secure way can be carried out without the manufacturer of the device or third parties can find out.
The next main point of investigation is the secure firmware updates via LoRaWAN. There is currently no official standard regarding the transfer of firmware. Updates via LoRaWAN. In this respect, it is one of the main tasks of this work
to design and test. In the end, the smart mailbox should be able to carry out firmware updates via LoRaWAN without user intervention. These updates must also be cryptographically secured to prevent manipulation. Finally, it is examined how mail is thrown into a mailbox device that can be recognized. Various technologies were examined and a suitable one was identified.
2.1 LoRaWAN
LoRaWAN is a LoRaWAN solution for IoT applications with a small amount of data energy-efficient and can be transmitted wirelessly over large distances. It consists of the one hand of LoRa radio, a protocol for physical data LoRaWAN transmission and on the other hand of LoRaWAN itself, a MAC protocol which is based on LoRa builds up and provides a standardized procedure for the transfer of data via LoRa. LoRaWAN, as one of the key points in this work, was used for communication with the end devices, including the smart mailbox.
2.1.1 What is LoRa
LoRa is a frequency modulation process developed by Semtech wireless communication between two communication partners allowed. It is, therefore, a physical protocol (OSI Layer 1), which only takes over the modulation of the physical data transmission. LoRa uses frequency-modulated chirps to encode symbols. The chirp modulation used uses “chirps” to transmit symbols. The frequency is continuously changed across the bandwidth over a defined period of time. The symbols transferred are about the beginning of the chirp are defined.
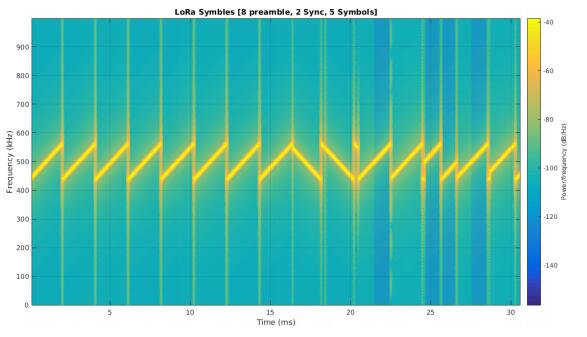
The primary advantages that this modulation offers compared to FSK or PSK are the long-range and the robustness against noise. Both are from the spreading factor and bandwidth used. The spreading factor determines how long a single chirp lasts, ie how wide it is spreading”. A higher factor means wider symbols, which ensures longer LoRaWAN transmission ranges, but also slower data transmission. In LoRa spreading factors from 7 to 12 is defined, which means LoRaWAN transmission speed from a maximum of 37.5 kbit / s to a minimum of 300 bit / s can be achieved. The bandwidth is fixed at 125 kHz, 250 kHz or 500 kHz and also influences the range and speed of the signal. The concrete choice of these parameters is determined by LoRaWAN.
The frequencies that LoRa uses depend on the region. In Europe, you can 868 MHz or at 433 MHz can be sent. It is important to mention that these frequencies are license-free spectra, so there is no license fee to use them. To compensate for this, apply temporal, send restrictions that all devices must adhere to. These are between 0.1% and 10%, depending on the frequency used.
2.1.2 What is LoRaWAN
LoRaWAN is a MAC protocol (OSI Layer 2), which is based on LoRa (but also with FSK can be used), and also some elements of a network protocol (OSI Layer 3) contains. It defines a message format, as well as MAC commands to control the transfer. The parameters for the underlying LoRa transmission are also determined by LoRaWAN. The first part is the actual specification, which defines the message formats, the MAC commands, and the sequence. The regional parameters, which specific settings for LoRa, as well as some adjustments or additions to the LoRaWAN protocol, are available as an extension define depending on the respective region.
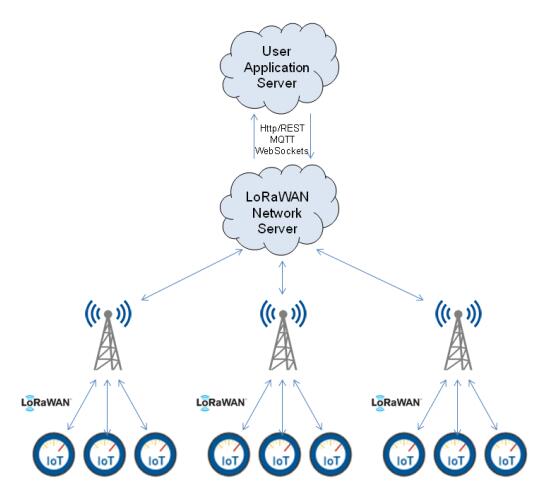
A LoRaWAN network consists of several groups of participants and is organized in a star-by-star topology, as shown in Figure 5. In the middle is the network server, which is the server-side administration of the LoRaWAN network and offers an API for client applications. Manage LoRaWAN applications and both send and send messages to receive. This server communicates with several gateways via an IP connection. Their primary task is to forward the LoRaWAN packets received from the network server to the end devices via LoRa and vice versa. Accordingly, they serve as an interface for changing the physical medium. Stand at the end than the end devices that communicate with one or more gateways to transmit their data. The LoRaWAN protocol is only between the gateway and the end devices used. No standard is defined for the remaining paths and that format, therefore, depends on the specific applications used.
In this context, LoRaWAN takes on some tasks, which are explained further below. This includes the different communication classes that are used data can be transmitted in different ways, the two options for adding devices to a LoRaWAN application, the encryption and integrity check of transmitted data, and the various MAC commands for controlling the connection. The latter will not be explained further because they are very specific and are not relevant to this work.
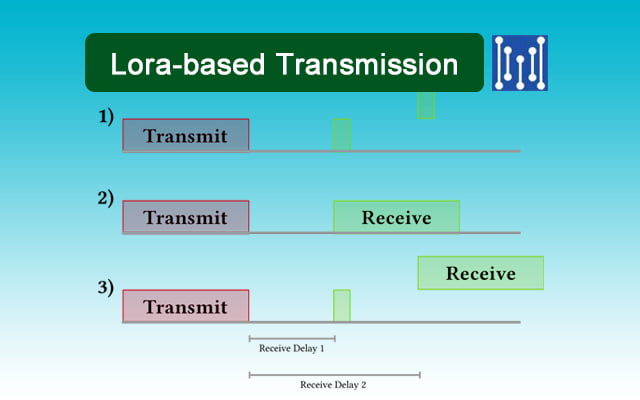
2.1.3 LoRaWAN Data transmission modes
LoRaWAN supports three different modes for data transmission. Each of these Modi has specific use cases, as well as advantages and disadvantages, which are listed below.
Class-A
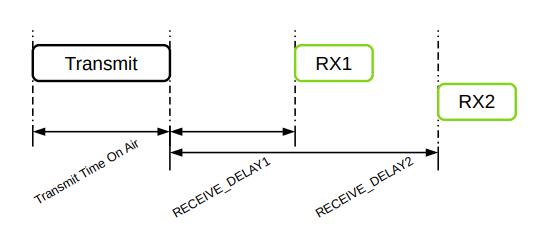
Class-A mode is the primary LoRaWAN transmission mode used by all end devices and gateways must be supported. It allows bidirectional communication between terminal and gateway based on the ALOHA principle. In the case of LoRaWAN, this means a terminal can send data at any time, but only for two short one’s Intervals after sending a data packet can also receive data.
The advantage of this mode is that a terminal device only while sending data and shortly after this turn on the LoRa transceiver to receive a response got to. This means that it can remain deactivated most of the time, which saves energy. The disadvantage, however, is that the terminal does not have any data at all other times can receive. In addition, only one can be received for each data packet sent become.
Class A operation, therefore, makes the most sense when primarily sending uplink messages and rarely downlink messages. Since LoRaWAN preferably in sensors and similar low-performance end devices that normally only provide status information for an end application is used for most end devices the preferred data transfer mode.
Class-B
Class-B is an extension that does not have to be supported by end devices. By this mode can be used by end devices in addition to Class-A at regular intervals. Receive data from the gateway without first having to send it yourself. To the beacon sends a so-called beacon every 128 s, which contains some status information about the gateway. End devices that receive this can then use the beacon and the ping slot periodicity to calculate the times at which data can be received. This allows them to be at the right time for short moments switch on the LoRa transceiver to receive any data that may be present. The process is shown below.
![]()
Class-B offers a good balance between accessibility and energy consumption since the ping slot periodicity can be adjusted to control how often it should be received. This means that more energy is used than for pure Class A operation, but there are still long periods in which the LoRa transceiver can be turned off. Another advantage of Class-B is the ability to store data in 8 to be able to transmit multicast to several devices simultaneously, as long as the address and the keys are the same. Multicast groups can, therefore, be created.
The use of Class-B makes sense if a device has to receive data more often without sending data itself, but the device still has to work energy-efficiently. A typical application would be end devices that are regular can be controlled without being time-critical.
Class-C
The last, also optional, the transmission mode is Class-C. In this, the switches terminal permanently on reception to be able to receive data from the gateway at any time. The option of transmission with Class-A remains as in the picture below.
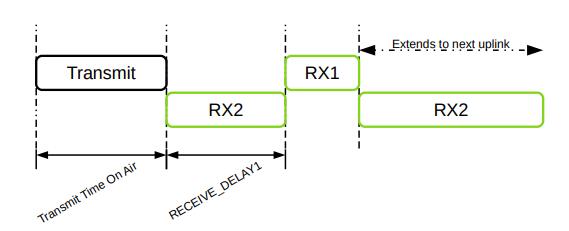
The advantage of Class-C is that data can be received at any time. However, the price for this is high energy consumption, since the end device must keep the LoRa transceiver active at all times. Multicast LoRaWAN transmission is also possible here.
Class-C should only be used when large amounts of data have to be transferred over a short period of time or when time-critical transfers occur. Such end devices should have a permanent power supply since this mode consumes too much energy for battery operation.